About Risk Management Enterprise
Wiki Article
The Main Principles Of Risk Management Enterprise
Table of ContentsRisk Management Enterprise - TruthsNot known Incorrect Statements About Risk Management Enterprise Risk Management Enterprise Things To Know Before You Buy
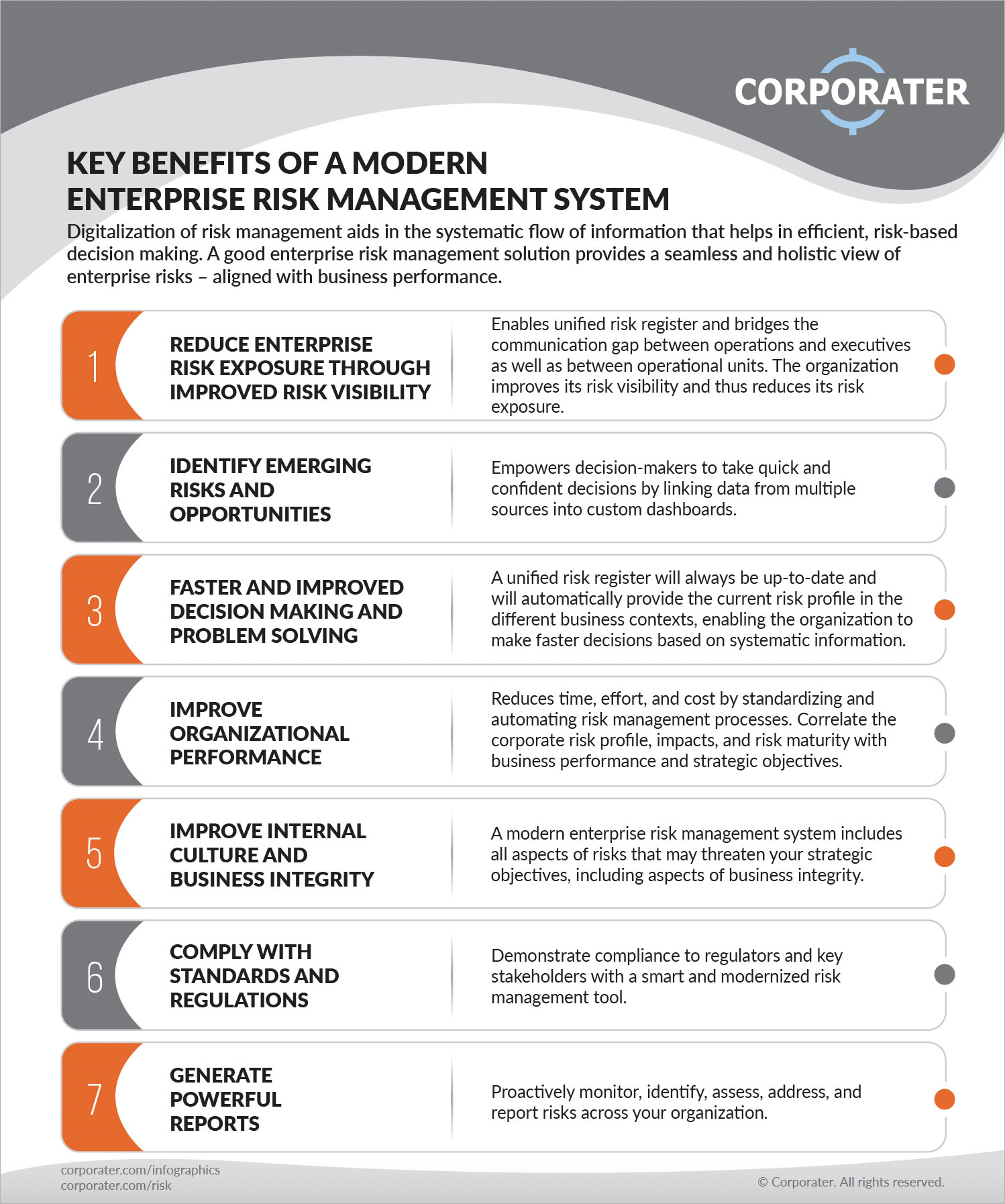
Control that can check out or modify these elements by setting particular access legal rights for private customers, making certain details security and customized usability. Permits users to tailor their user interface by picking and organizing important data elements. Supplies a tailored experience by permitting customization of where and exactly how information components are shown.It enables access to real-time integrated data instantaneously. Risk Management Enterprise. This assists eliminate thrown away time on hand-operated record compilation. Also, centers can make use of detailed data intelligence for quicker and extra educated decision-making. It enables the automated development of stakeholder reports for people or groups. Makes it possible for prompt decision-making and decreases hold-ups triggered by outdated info.

Diligent is a risk management software that permits maximizing performance, and increases growth. It additionally aids keep an eye on threats with ERM software program that includes integrated analytics and adapts to your organization requirements. This software application comes with numerous beneficial functions. Below we have actually highlighted the most important ones. Examine them out.
Not known Details About Risk Management Enterprise
It likewise gives one-click reports. Additionally, it offers your leadership and board the real-time insights they require. Simplifies the process of accumulating threat data from different components of the company. Risk Management Enterprise. It enables very easy personalization of records and storyboards. Provides leadership and the board with real-time danger understandings. Usage ACL's innovative analytics to spot danger patterns and anticipate hazards.This look what i found enables business to catch danger understandings and red flags in the third-party vendor's safety record. This enables conserving threat analyses as auditable documents. It additionally permits exporting them as PDFs. To finish the procedure business can complete a reassessment date. Enables companies to capture and record threat understandings and red flags in third-party vendor protection reports.
Identifying risks ahead of time aids a Web Site center plan for audits. It likewise decreases threat via streamlined compliance and threat administration. Due to this centers will not have to handle different systems for risk monitoring. The users of Hyperproof can systematize danger management in one area. It can assist collect and track all your threats in the Hyperproof risk register.
It makes certain that whatever is arranged and easily accessible for auditors. Utilizes automation to maintain proof updated while reducing hands-on initiative. It offers fast access to needed details and documents. This makes certain the safety and security of Active proof instances by making it possible for multi-factor authentication (MFA) making these details use of authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy.
The Buzz on Risk Management Enterprise
It gives top-tier protection attributes to guard sensitive data. This danger management software application is an ideal tool for facilities looking to take care of unnecessary problems or dangers.
Users can also utilize the AI-powered devices and pre-existing web content to produce, review, prioritize, and address threats effectively. Enhances the procedure of setting up and occupying threat signs up. Makes use of AI and library web content to boost threat analysis precision. It enables quicker identification and reduction of dangers, This is mostly an aesthetic model.
Report this wiki page